Detection Group Key🔗
Note
The terms Alerts and Investigations have recently been changed to Detections and Cases in Taegis XDR. You may still see references to the old terms while we continue to work towards platform convergence of Sophos and Taegis technologies. For more information, see Taegis Terminology Updates.
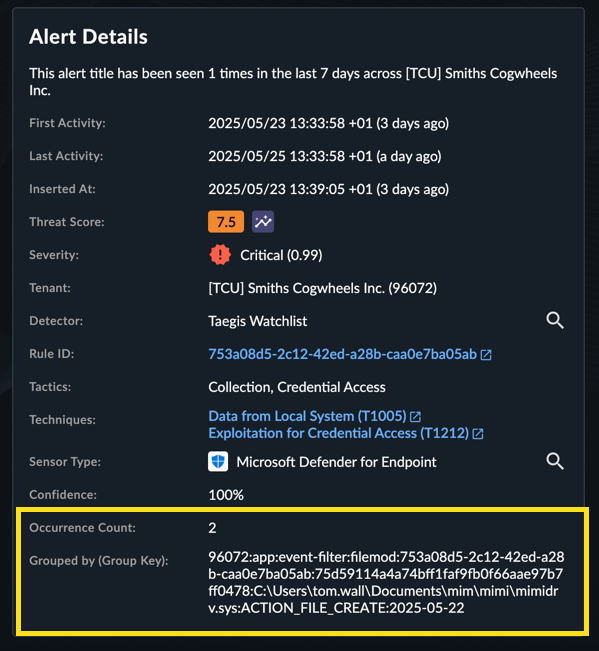
To reduce the volume of detections, Secureworks® Taegis™ XDR detectors may use the detection group key to create one detection per key within a specified time window. These group keys are intended to deduplicate detections which are primarily identical, except for timestamp and other non-consequential fields. Grouped detections contain a total occurrence count, first seen timestamp, last seen timestamp, first event, and last event.
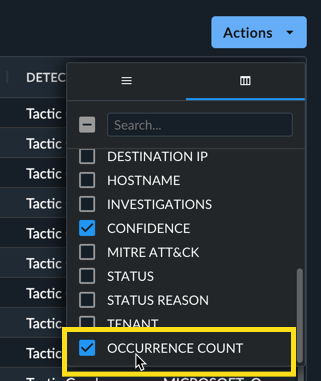
The Detection Details Summary tab contains Occurrence Count and Group by (Group Key) fields. In addition, the JSON tab contains the object events_metadata which contains the first and last event associated with the detection.
Occurrence count is available on the detection tables contained in the following pages:
- Detections
- Detection Search
- Case → Evidence → Detections
FAQ🔗
Why are there only two events available in the detection JSON?🔗
The JSON view of the detection will contain the first event ID and last event ID that occurred. All event occurrences are searchable and appear in the detection details Events tab.
What is the group key?🔗
A group key is configured per watchlist and contains fields from the events contained in the detection. For example, a NIDS group key is made up of the following fields.
- Tenant ID
- Sensor Type
- Detection Title
- Source IP
- Destination IP
- Date (24 hour window)
What detection types have this group key capability?🔗
All detections use group keys to aggregate repeated occurrences.
How does the seven-day group key work?🔗
Detections for rules configured with a seven-day group key are grouped to a single day from Monday to Friday. All detections generated by the associated rule are deduplicated to the same day of the work week.
Example🔗
- Rule one is set to deduplicate on Monday.
- This rule creates a new detection on Friday.
- Repeated occurrences on Saturday and Sunday are appended to the detection created on Friday.
- On Monday, repeated occurrences generate a new detection, and occurrences are appended until the next Monday.
- The next Monday, a new detection may be created.
What changed with the Detection schema?🔗
The detection schema now contains group_key and an events_metadata object.
"events_metadata":{
"__typename":"AlertEventMetadata",
"began_at":{
"__typename":"Timestamp",
"nanos":0,
"seconds":1661119511
},
"ended_at":{
"__typename":"Timestamp",
"nanos":774000000,
"seconds":1661286639
},
"first_event_id":"event://priv:scwx.nids:35959:1661272095206:146d8128-d2fb-5d06-ac20-8dd7bac30763",
"last_event_id":"event://priv:scwx.nids:35959:1661286639774:146d8128-d2fb-5d06-ac20-8dd7bac30763",
"total_events":9,
"updated_at":{
"__typename":"Timestamp",
"nanos":391062,
"seconds":1661287835
}
},
"group_key":[
"35959:Cisco eStreamer:SERVER-WEBAPP GPON Router authentication bypass and command injection attempt:2.2.3.3:1.1.1.4:2022-08-21"
],