Identity Details🔗
Identity Details provides pertinent information about the identity based on the data collected from your Identity Provider as well as observations across your Secureworks® Taegis™ XDR data sources.
To view Identity Details, select the Display Name from the top of a card or from the table on the Identities view of the Directory page.
Identity details are organized into the following tabs:
Summary Tab🔗
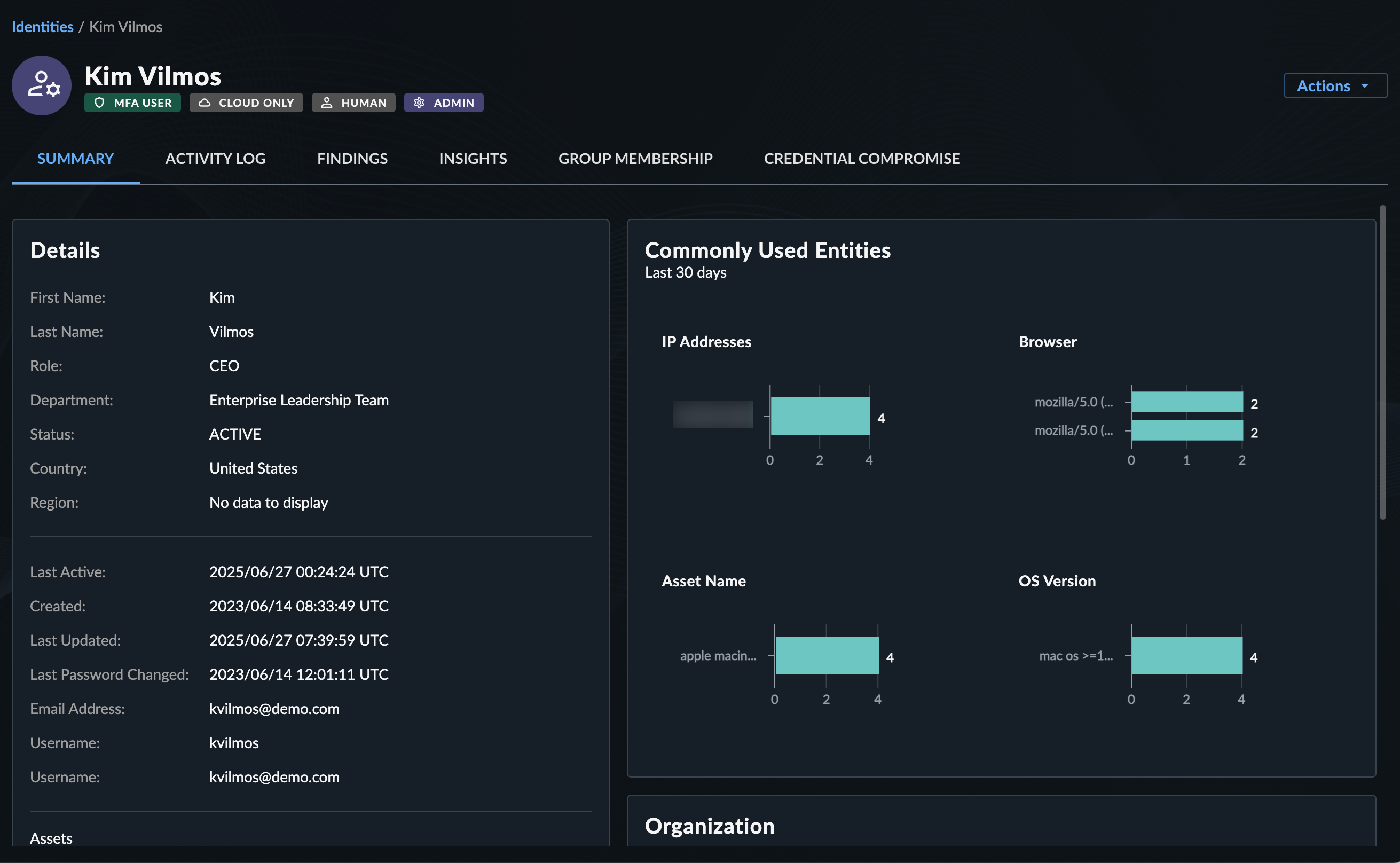
The Summary tab presents the following identity information:
Details🔗
The Details section contains details about the identity as available from your Microsoft Entra ID environment. This includes information about their role, department, status, country, and region. Additionally included are details of when their account was created and updated, the last password change time, and other related email addresses associated with the user.
Related Devices🔗
The Related Devices section contains Intune devices that are associated to the user within Microsoft Entra ID.
MFA🔗
The MFA section contains details about the MFA (Multi-factor Authentication) configuration of the user, such as the MFA provider, primary MFA method, and any other MFA types configured.
Recent Detections and Cases🔗
The Recent Detections and Cases section contains tabs with the following information:
- Open Detections — Open detections within the past seven days for the identity
- Closed Detections — Closed detections within the past 30 days for the identity
- Cases — Open or closed cases within the past 30 days for the identity
Select the View All button from within Recent Detections and Cases to navigate to the Insights tab.
Commonly Used Entities🔗
The Commonly Used Entities section provides insights into some of the attributes related to successful authentications over the last 30 days. This helps you understand the profile of the user and what is common or abnormal. The following graphs display when we have data for the user:
- IP Addresses — The IP addresses that we have observed the user successfully authenticating from
- Browser — The user-agents that we have observed the user successfully authenticating from
- Asset Name — The types of assets that we have observed the user successfully authenticating from
- OS Version — The operating system version that we have observed the user successfully authenticating from
Organization🔗
The Organization section provides a snapshot of the identity's reporting structure. This allows you to see who the individual reports to and whether or not they also have direct reports. This is useful when investigating threats or formulating a risk assessment of the user and its related activity. Click the organization chart to open other users in a new window.
Activity Log Tab🔗
The Activity Log tab displays tables of events across any configured data sources related to the identity. Select an event type from above the table to switch between the types and select an event summary from the table to view more details.
Findings Tab🔗
The Findings tab displays a table of findings related to the specific identity sorted by risk.
- Hover over the Recommendation field to view the full recommendation.
- Select the finding name to open the finding details.
Insights Tab🔗
The Insights tab displays the following information:
- Open Detections — Open detections for the identity within a default period of the past seven days; use the date picker at the top of this section to change the period
- Closed Detections — Closed detections within the past 30 days for the identity
- Cases — Open or closed cases within the past 30 days for the identity
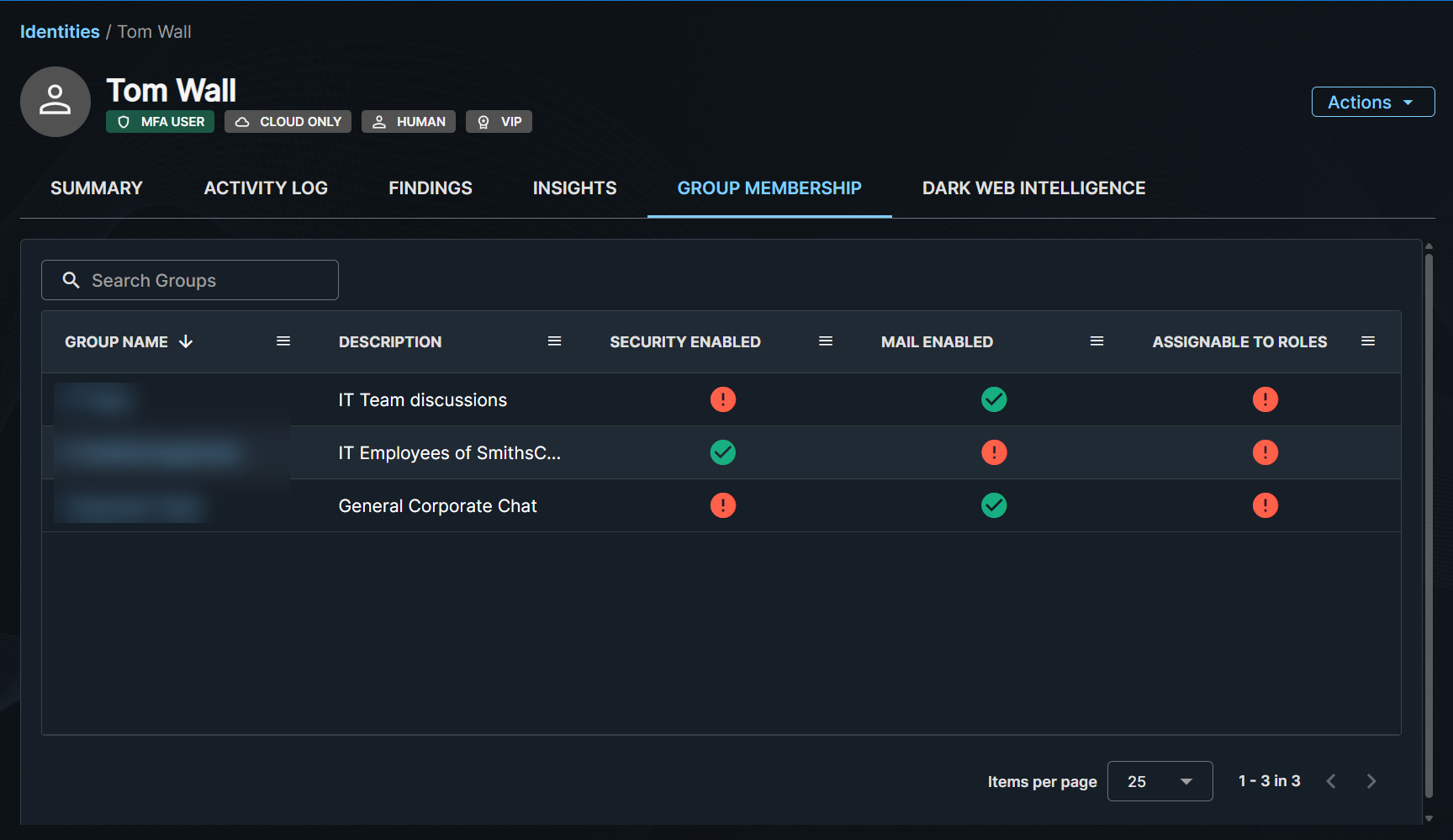
Group Membership Tab🔗
The Group Membership tab displays the list of groups the user is part of. Use the search field to search for groups and select Group Name field to open the group in a new page to view other members.
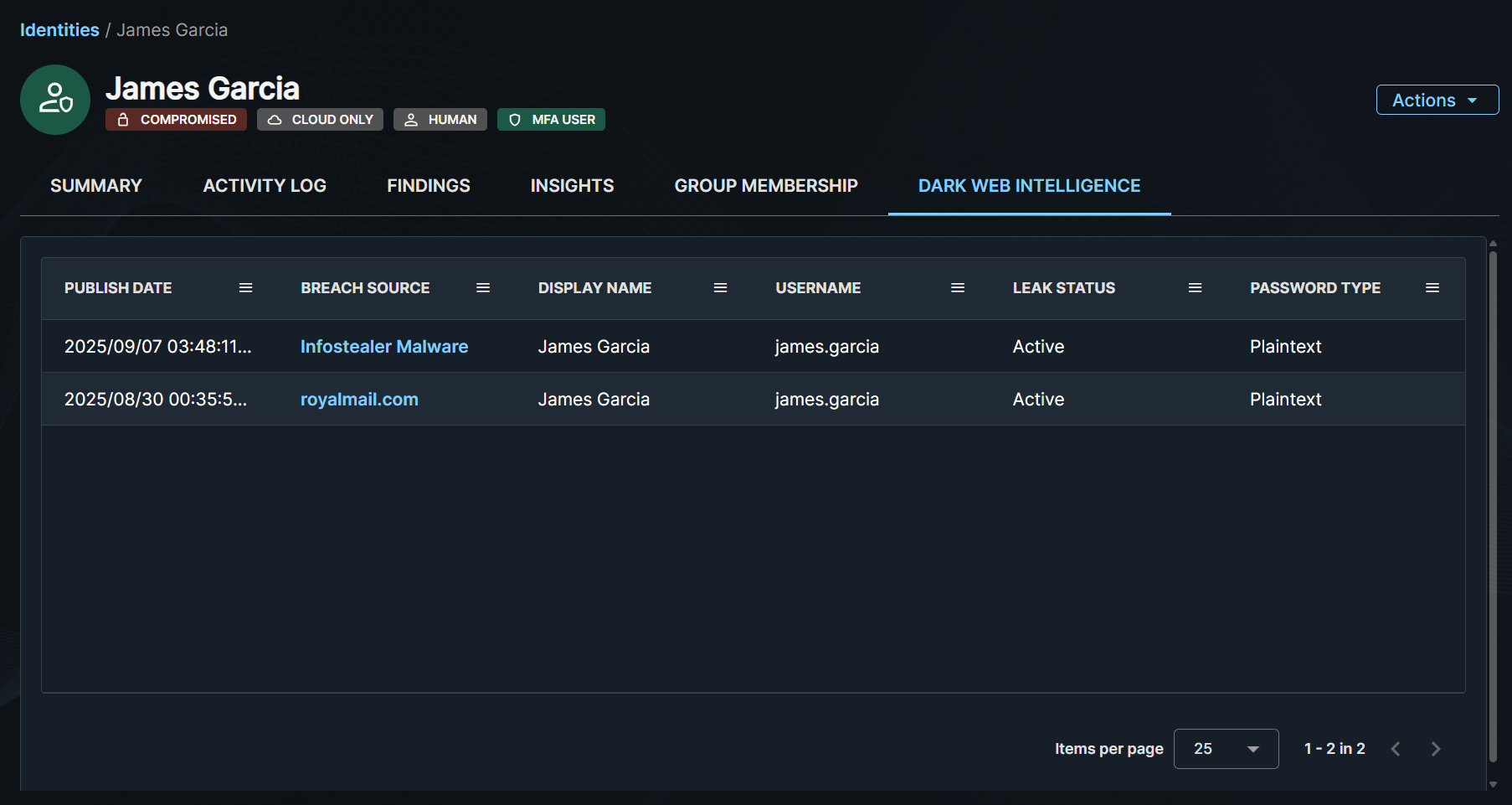
Dark Web Intelligence Tab🔗
The Dark Web Intelligence tab displays a list of breaches to which the identity is linked. Select the link from the Breach Source field to view additional details about the breach record. For more information, see Dark Web Intelligence.