Detection Suppression Rules🔗
Note
The terms Alerts and Investigations have recently been changed to Detections and Cases in Taegis XDR. You may still see references to the old terms while we continue to work towards platform convergence of Sophos and Taegis technologies. For more information, see Taegis Terminology Updates.
You can create detection suppression rules that resolve detections as suppressed when they're created so that they don't show by default on the Detection Triage Dashboard but can still be found in searches.
Important
Suppressed detections are not triaged by Secureworks analysts.
Tip
The Secureworks Professional Services team is here to help you realize the full potential from your Taegis XDR investment if a higher level of support is desired. Our highly skilled consultants can help you deploy faster, optimize quicker, and accelerate your time to value. For more information, see Professional Services Overview.
View Detection Suppression Rules🔗
- From the Taegis Menu, select Detections > Customization Rules. The Custom Rules table displays.
- Select the Suppression Rules tab to view all of the current suppression rules.
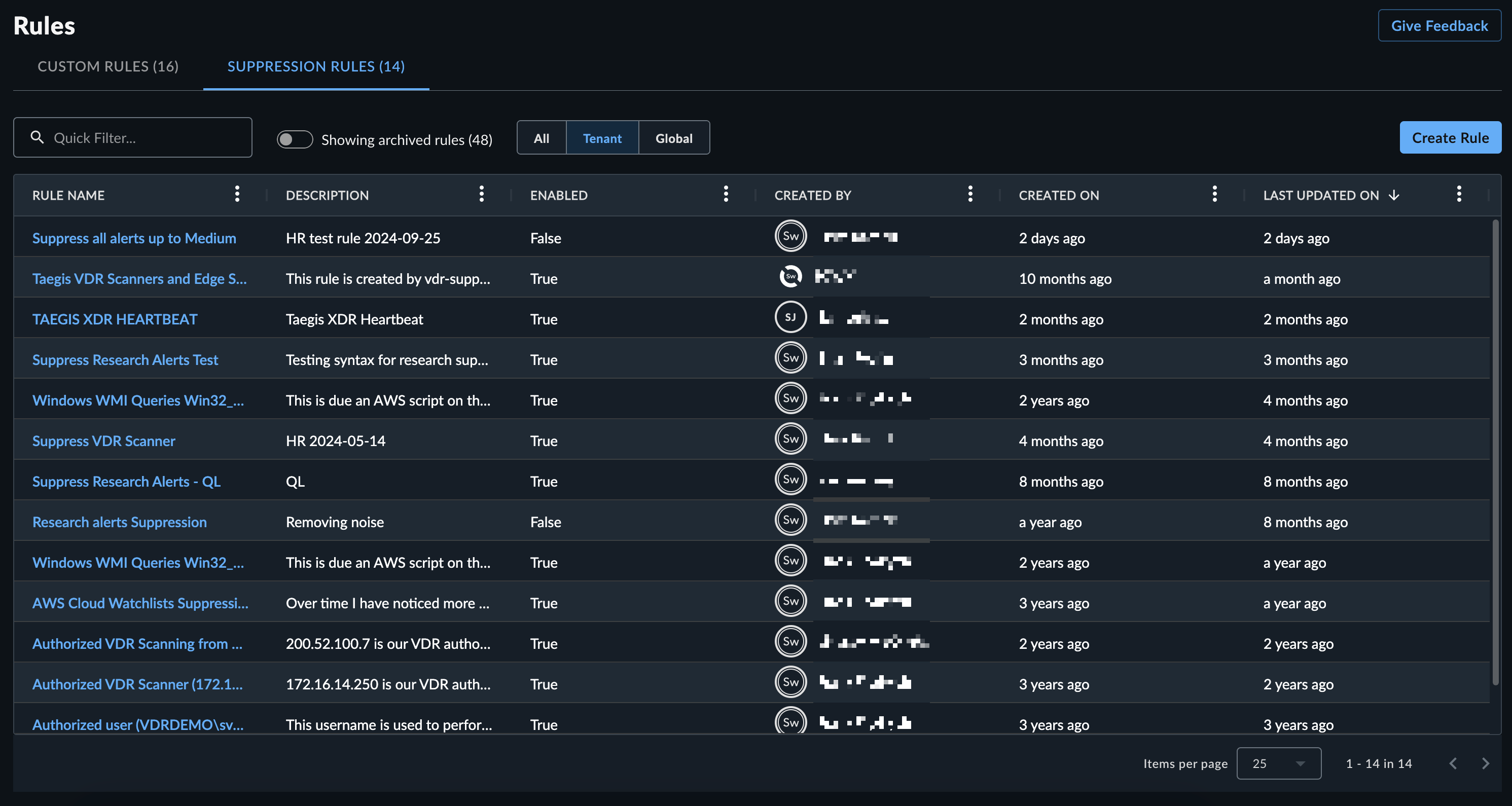
Tenant rules are specific to the tenant and only suppress detections for that individual tenant. Global rules apply to ALL XDR tenants. Global rules are commonly created to triage detection floods until the detection rule or detector is tuned. Global rules are read-only. Please contact support if you have questions about a global rule.
Create Suppression Rules🔗
You can create a detection suppression rule in one of the following ways:
Query Language Method🔗
Suppression rules support matching on a detection's underlying event data using Advanced Search query language. For example, suppression rules can use query language elements such as process.commandline, process, parent_image_path, and other event schemas.
Note
See the FAQ for additional information.
Use advanced search first to create the query that targets the desired detections before you create the suppression rule.
- Build your Advanced Search query to verify which past detections are to be suppressed in the future. When you are satisfied with the results, copy the query to paste into the rule builder.
- Go to Detections > Customization Rules and select the Suppression Rules tab.
- Click Create Rule above the Suppression Rules table.
-
In Create Suppression Rule, paste the Advanced Search query that targets the desired detections in the Rule Criteria field.
Tip
Click See potential matches with current data in the right pane to test your query and verify it targets the desired detections.
-
Enter a Name and Description for the rule.
-
Select the resolution status you want detections that match this rule to be labeled with.
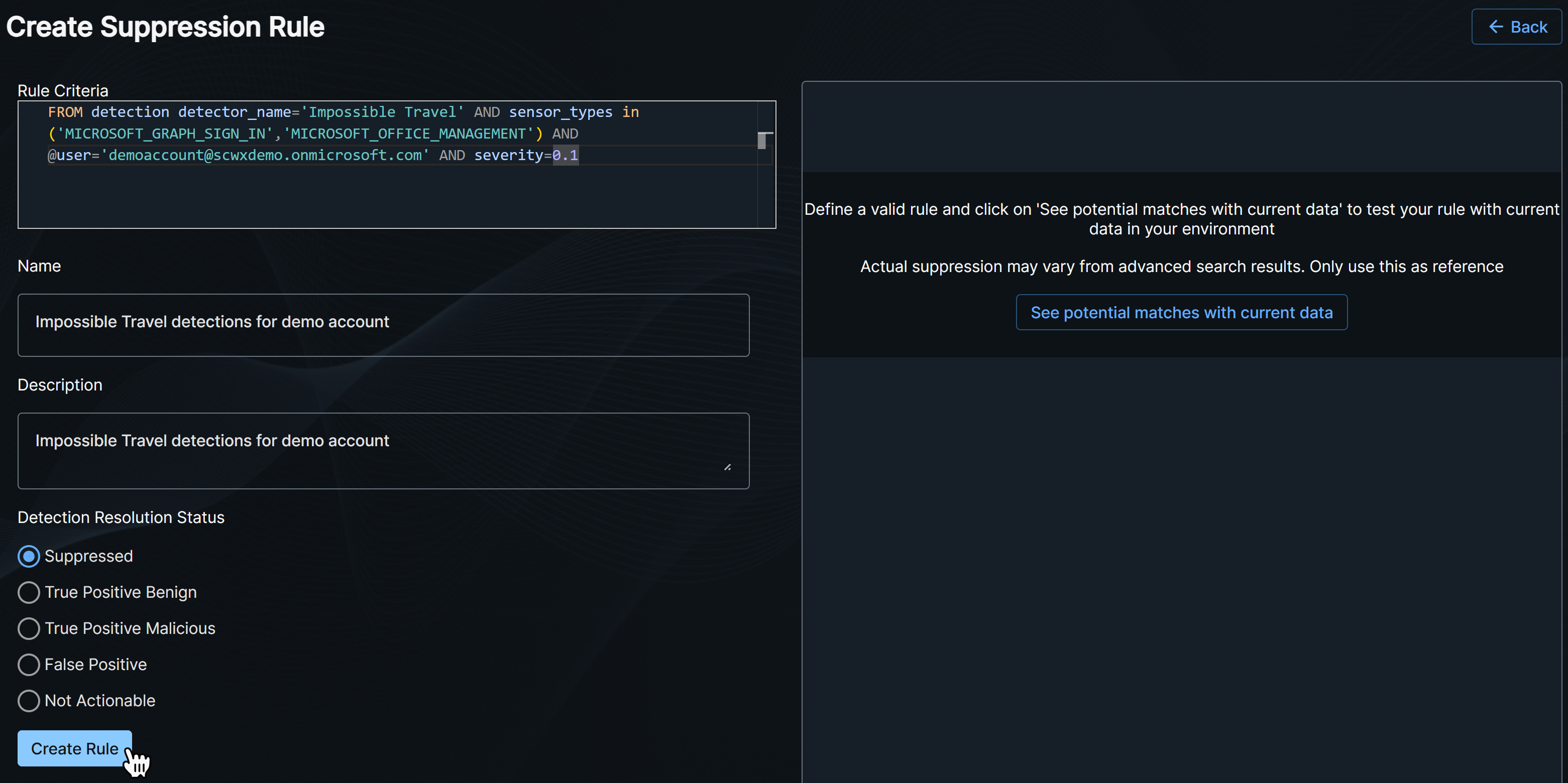
Create a Suppression Rule with Query Language -
Click Create Rule.
Detection Method🔗
- Open the details of a detection you want to suppress.
- From the detection details page, select Actions > Create Suppression Rule.
-
The Create Suppression Rule form populates with entities from the detection. Select one or more entities to build your rule, or manually add criteria.
- Multiple criteria are joined with an
ANDoperator. - Criteria use PCRE regular expressions to perform matching.
- Suppression rules run queries against streaming data and Primitive Fields do not automatically get default values, which differs from data stored in the Taegis data lake and queried by Data Lake Search. In suppression rules, you can use the NULL operators to check if these Primitive Fields are set.
- Regular expression special characters are automatically escaped when you use the prepopulated entities. If you manually add criteria, you must escape these characters. See the following note for more details.
Note
The following characters have special meaning within regular expressions:
. ^ $ * + - ? ( ) [ ] { } \ | /. For IP addresses, domain names, and other instances, take care to escape the characters with a backslash:1\.1\.1\.1.
To escape long sequences that contain multiple characters, enclose the whole string between\Qand\Eso that the string is not evaluated for regex characters. For example, escaping this full string:
\Q${jndi:ldap://log4shell-smb-21yg3cbuy21gbcy21gc321uc${lower:ten}.w.nessus.org/nessus}\E
is equivalent to:
\$\{jndi:ldap:\/\/log4shell\-smb\-21yg3cbuy21gbcy21gc321uc\$\{lower:ten\}\.w\.nessus\.org\/nessus\} - Multiple criteria are joined with an
-
Enter a Name and Description for the rule.
-
Select the resolution status you want detections that match this rule to be labeled with.
Create a Suppression Rule from a Specific Detection -
Click Create Rule.
View Suppression Rule Details and History🔗
Select a rule name from the Suppression Rules table to view its details and history.
Suppression Rule Details🔗
The Details tab of the suppression rule contains overview information for the rule with the criteria the rule matches on. You can edit the rule name, criteria, description, and resolution label from this view.
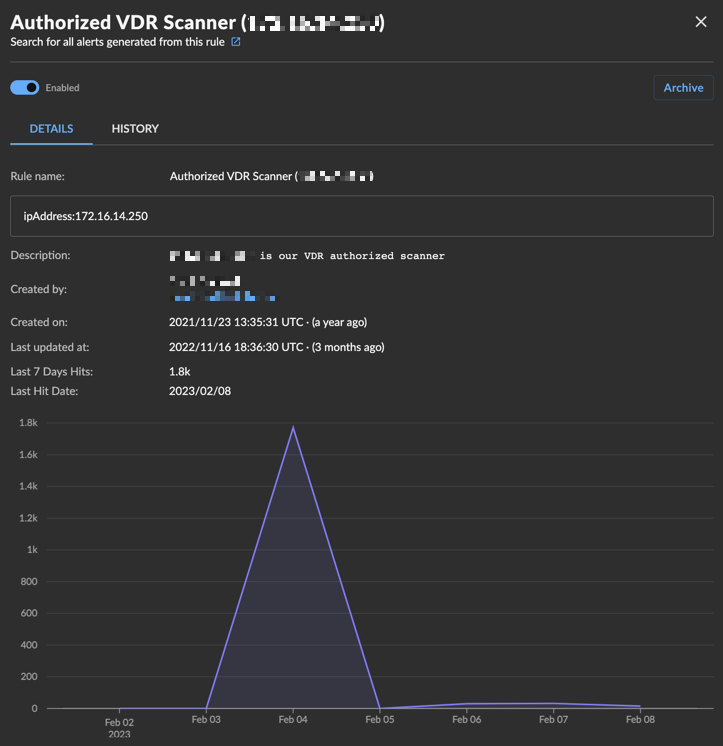
If the rule has matched on and suppressed detections in the last seven days, the following display:
- Number of hits in the last seven days
- Last hit date
- Line graph visualizing the amount of hits
If there has been no activity in the last seven days, this section does not display.
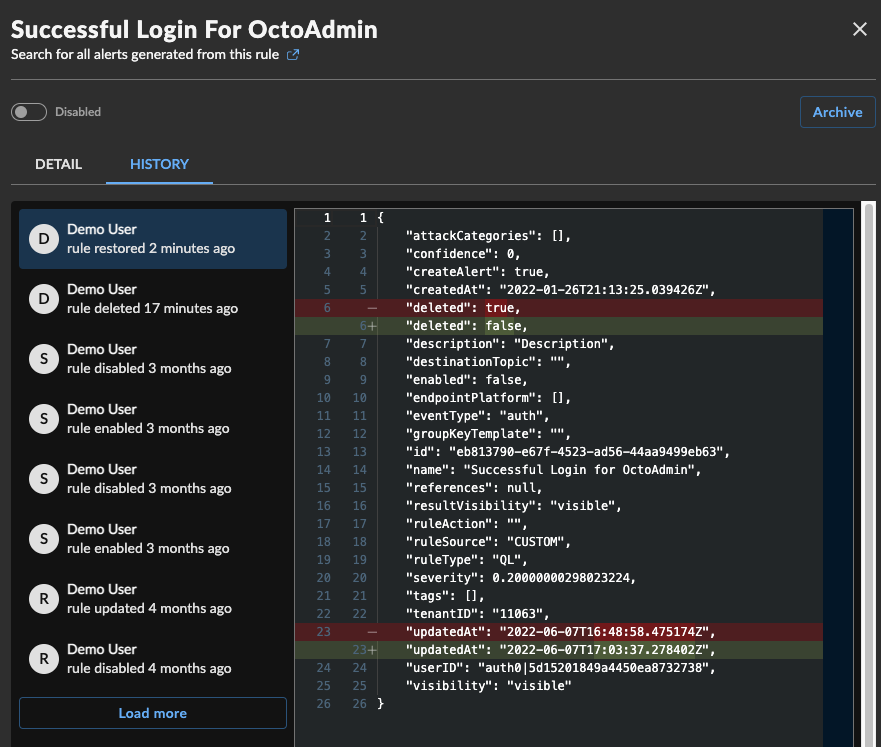
Suppression Rule History🔗
The History tab of the suppression rule contains a changelog of edits to the rule. Choose an audit log from the list on the left to view the diff in the right pane.
Archive and Restore a Suppression Rule🔗
When viewing a suppression rule, you can archive the rule by selecting Archive and confirming the action. This disables the rule, marks it as archived, and removes it from the default view of the Suppression Rules table.
To view archived rules, select Showing Archived Rules above the table.
When viewing an archived suppression rule, you can restore the rule by selecting Restore and confirming the action. This restores the rule in a disabled state and returns it to the default view of the Suppression Rules table. Select the toggle to enable the rule.
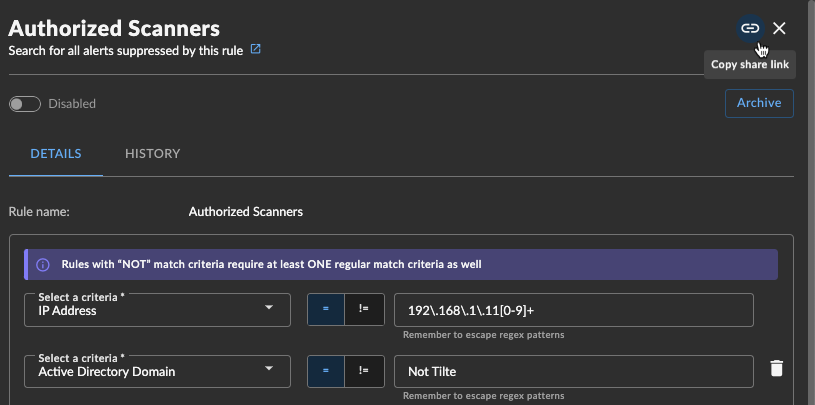
Share a Suppression Rule🔗
To share a suppression rule with another user within the tenant, select the Copy share link icon from the rule details for a direct URL.
Common Detection Suppression Rules🔗
Authorized Scanner🔗
Use Source IP Address to suppress detections originating from an authorized scanner.
If you have multiple authorized scanners, use a regular expression to include all IP addresses into one suppression rule.
Guest Network Range🔗
Use Source IP Address to suppress detections from a guest network range, using a regular expression to match the entire network range.
Authorized Process Execution on Endpoint🔗
Use a combination of patterns to match both the endpoint and process.
-
Use one to match endpoint:
- Sensor Host ID
- IP Address (if host has a static IP address and does not have an endpoint agent installed)
-
Use one to match the process:
- File Name
- File (MD5|SHA1|SHA256|SHA512)
- Program Name
- Program (MD5|SHA1|SHA256|SHA512)
- Script SHA1 (This is a hash of the executed script)
FAQ🔗
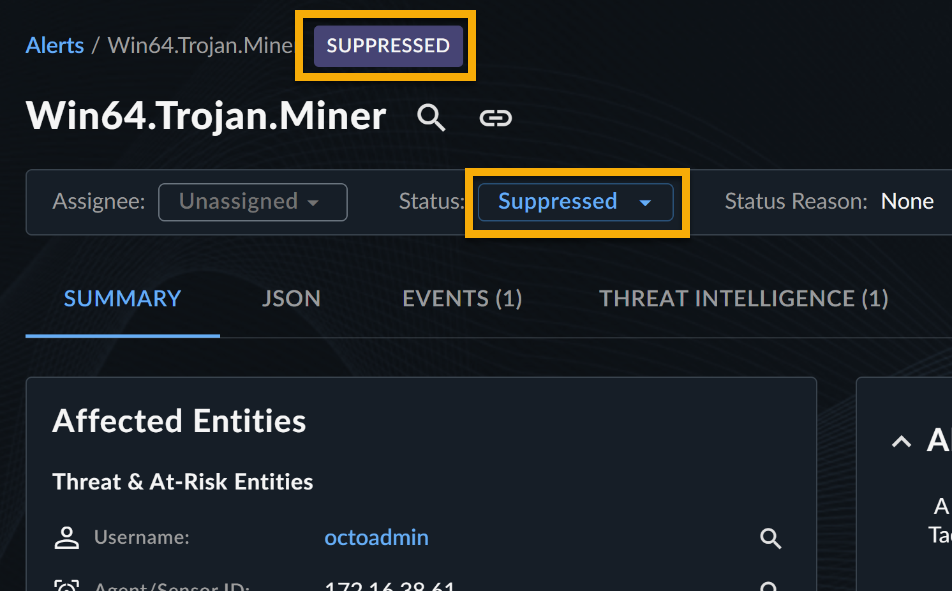
How do I know if a detection has been suppressed?
Suppressed detections are marked with a feedback label of Suppressed.
How can I search for suppressed detections?
Suppressed detections have the feedback label Suppressed. You can search for them using the following query:
To exclude suppressed detections from your results, add a NOT to the labelName criteria match:
Another method is to run a pivot search from the rule itself. Open a rule and select the new tab icon next to Search for all alerts suppressed by this rule. This opens up an advanced search that queries for detections that were suppressed by this specific rule.
Can I add suppressed detections to a case?
Yes, suppressed detections can still be added to new or existing cases.
Can I change the feedback label on a suppressed detection?
Yes, in the detection details view, you can remove the feedback label or change the label.
Can I audit rule manager activity?
Yes, actions in the rules manager are viewable by navigating to Tenant Settings > Audit Logs. Audit logs will have the category of Rules.
Additionally, a changelog of edits to the rule is available from the rule itself. See View Suppression Rule Details and History.
When a detection is suppressed, how do I know which rule suppressed the detection?
When viewing detection details, click the rule name in the Suppression Rule field to view the rule in a side panel.
What regular expression features do the rules support?
The detection suppression engine utilizes Hyperscan to apply regular expressions. Hyperscan supports the pattern syntax used by the PCRE library libpcre, described at http://www.pcre.org/. However, not all constructs available in libpcre are supported. The use of unsupported constructs will result in compilation errors.
For more details, see Hyperscan Developer Reference Compilation.
For domain names or IP addresses, do I need to do anything special to handle the dots?
Yes, you need to escape the dots using a backslash. In regular expressions, a dot means to match any single character except newline.
Example: 192\.168\.1\.1 or www\.secureworks\.com
What entities can I match against?
The best way to build a suppression rule is to leverage entities listed on an existing detection. To view entities available on a detection when viewing detection details:
- Go to the JSON tab.
- Expand the entities JSON object.
-
Observe entities listed on the detection.
Note
If the detection does NOT have entities, that detection is not able to be suppressed yet at this time. Efforts are under way to add detection suppression to all detection.
Detection Entities
When building your rule, you can pick entities from a drop down. The following entities can be used to create detection suppression rules. Unique entities are parsed from the individual events included in the detection.
| Entity Prefix | Entity Description |
|---|---|
| authDomainName | Active Directory Domain |
| sourceUserName | Auth Source Username |
| sourceAuthDomainName | Auth Source Domain Name |
| targetUserName | Auth Target Username |
| targetAuthDomainName | Auth Target Domain Name |
| computerName | Computer Name |
| decodedScriptSha1 | Decoded Script SHA1 |
| destHostName | Destination Hostname |
| destIpAddress | Destination IP Address |
| destIpGeo | Destination IP Geolocation |
| destMacAddress | Destination MAC Address |
| dnsName | DNS Name |
| fileMd5 | File MD5 |
| fileName | File Name |
| fileSha1 | File SHA1 |
| fileSha256 | File SHA256 |
| fileSha512 | File SHA512 |
| ipAddress | IP Address |
| city | IP Address Geolocation City |
| country | IP Address Geolocation Country |
| latLon | IP Address Latitude,Longitude |
| macAddress | MAC Address |
| programMd5 | Program MD5 |
| programName | Program Name |
| programSha1 | Program SHA1 |
| programSha256 | Program SHA256 |
| programSha512 | Program SHA512 |
| registryName | Registry Name |
| registryPath | Registry Path |
| scriptSha1 | Script SHA1 |
| sensorHostId | Sensor Host ID |
| sensorId | Sensor ID |
| sourceIpAddress | Source IP Address |
| sourceIpGeo | Source IP Geolocation |
| sourceMacAddress | Source MAC Address |
| topPrivateIpDomain | Top Private IP Domain |
| userName | Username |
| workstationName | Workstation Name |
Which detectors support detection suppression?
All detectors and detection sources support suppression.
Are there limitations to using query language for suppression rules?
The following detection schema fields are not supported at this time:
- enrichment_details
- third_party_details — use
thirdpartyevent schema instead - status
- case
How can I create a suppression rule for detections containing a specific commandline?
To suppress by commandline, use the process.commandline schema in the query language for the advanced suppression rule.
FROM detection WHERE process.commandline CONTAINS 'your_string'
How can I use detection entities in my suppression rules?
There are two ways to us the detection entities:
-
Use logical types in the query to include the desired detection entity. To suppress by hostname, use
@host.FROM detection WHERE @host='somehostname' -
Use the entities field directly; when viewing a detection you want to suppress, in the JSON view, open
entities.entities. Use the entire string to match against the desired entity. To suppress by destination IP address:FROM detection WHERE entities='destIpAddress:128.206.10.3'
How can I use IP CIDR ranges for suppression?
You can now use IPv4 CIDR ranges in your rule's query.
Note
Detection search does not support CIDR ranges, so these queries cannot be built using advanced search. We recommend that you build the query in advanced search without the CIDR ranges and then add the ranges when ready to create the suppression rule.
Note
IPv6 CIDR ranges are not supported in suppression rules at this time.
How do I suppress detections with IPv6 addresses?
Suppression rules support IPv6 addresses. When you use an IPv6 address in a suppression rule, the rule automatically normalizes the address so that it matches equivalent representations. For example, a rule that uses the compressed form also matches the uncompressed form, and vice versa.
You can match an IPv6 address in a suppression rule in three ways:
-
Logical type (e.g.,
@ip):FROM detection WHERE @ip = '2001:db8:85a3::8a2e:370:7334' -
Schema field (e.g.,
auth.source_address):FROM detection WHERE auth.source_address = '2001:db8:abcd:1234:0:1::' -
Entities (e.g.,
sourceIpAddress):FROM detection WHERE entities = 'sourceIpAddress:2001:db8:abcd:1234:0:1::'
In all three cases, the rule matches events regardless of whether the address was stored in compressed (e.g., 2001:db8:abcd:1234:0:1::), partially expanded (e.g., 2001:db8:abcd:1234:0:1:0:0), or fully expanded (e.g., 2001:db8:abcd:1234:0000:0001:0000:0000) format.
Note
- Suppression rules do not support IPv4-mapped IPv6 addresses (such as
::ffff:192.0.2.47) at this time. - Suppression rules do not support IPv6 CIDR ranges at this time. To suppress a range of IPv6 addresses, create individual rules or use a regular expression pattern with the detection method.