Check Point Harmony Email Security Integration Guide🔗
The following instructions are for configuring a Check Point Harmony Email Security integration to facilitate log ingestion into Secureworks® Taegis™ XDR.
Data Provided from Integration🔗
| Normalized Data | Out-of-the-Box Detections | Vendor-Specific Detections | |
|---|---|---|---|
| Check Point Harmony Email Security | Email, Thirdparty |
Note
XDR detectors are not guaranteed to be triggered, even if a data source's logs are normalized to a schema associated with a given detector. However, you can create Custom Detection Rules to generate detections based on normalized data from a data source.
Configure a HTTP Ingest Integration in XDR🔗
Tip
It is recommended that you create a HTTP Ingest integration for each source sending log messages to XDR. Separating data sources adds search flexibility, improves health monitoring, and accelerates troubleshooting.
-
Follow the XDR documentation to configure a HTTP Ingest integration.
-
Copy the Integration Key and URL to a secure location.
Configure Check Point Harmony Email Security🔗
-
Refer to the vendor's documentation to configure log forwarding to HTTPS.
-
Select Splunk HTTP Event Collector (HEC) as the Transport.
-
Enter the following values:
- HTTP Event Collector Host / URI: The URL generated when the HTTP Ingest integration was created.
- HTTP Event Collector Token: The Integration Key generated when the HTTP Ingest integration was created.
-
Select JSON as the Format.
-
Click Save.
Verify that Check Point Harmony Email Security is Sending Log Messages to XDR🔗
-
From the Taegis Menu, select Integrations → Cloud APIs.
-
Find the Harmony integration within the Cloud API Integrations table (e.g., using the Integration Name defined in the first section).
-
If the status is Healthy, XDR is receiving log messages successfully.
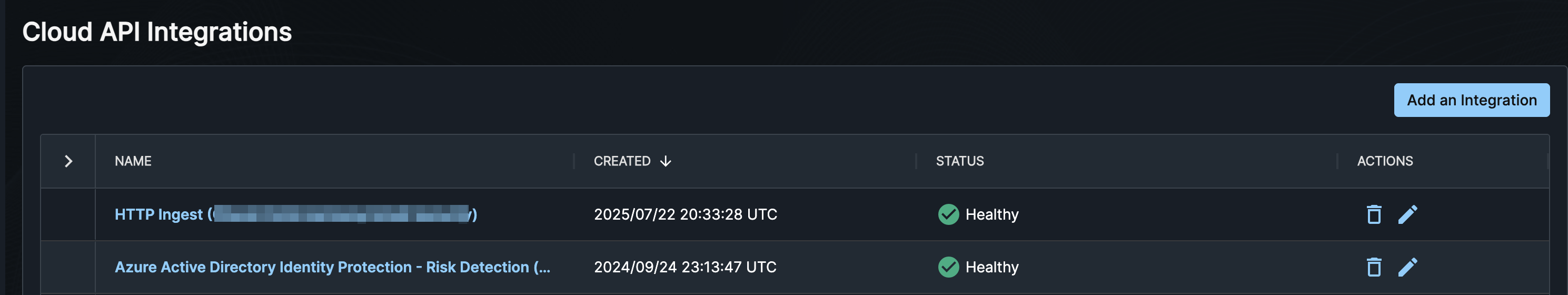
HTTP Ingest Health
Example Query Language Searches🔗
To search for email events from the last 24 hours:
FROM email WHERE sensor_type = 'Check Point Harmony Email' and EARLIEST=-24h
To search for email events that are classified as "phishing":
FROM email WHERE sensor_type = 'Check Point Harmony Email' and threats.classification = 'phishing'