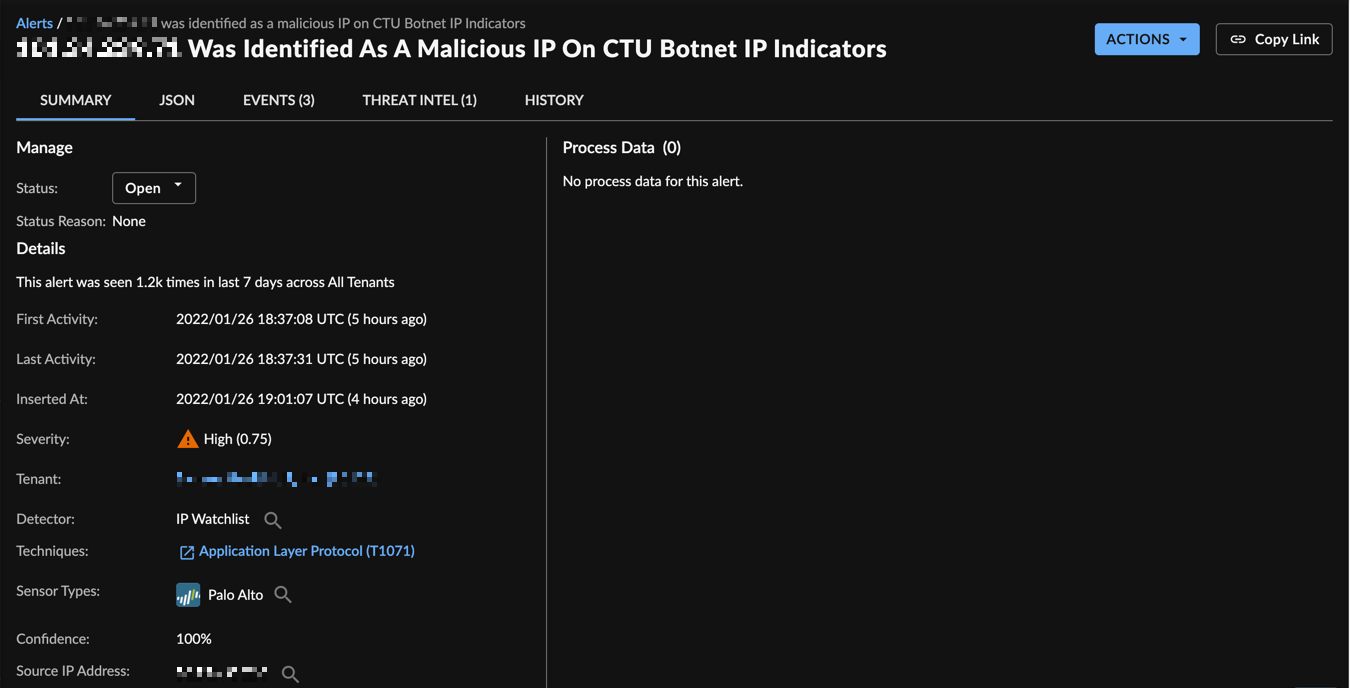
IP Watchlist🔗
The IP Watchlist Detector uses a Secureworks Counter Threat Unit™ (CTU) Threat Intelligence curated list of suspicious IP addresses and compares them to Netflow telemetry collected via supported endpoint and syslog data sources. When a suspicious IP is identified in tenant telemetry a detection is generated. The detection contains the list the suspicious IP was sourced from and the reason it is suspicious within the Detection Description.
Note
Taegis™ NDR automatically downloads the list of Secureworks malicious IP addresses and uses them within the reputation preprocessor to detect malicious traffic in real-time.
Requirements🔗
This detector requires the following data sources, integrations, or schemas:
- Netflow Source and Destination IP events
- Endpoint Netflow events
Inputs🔗
Detections are from the following normalized sources:
- Auth, Netflow
Outputs🔗
Detections from this detector are pushed to the XDR Detection Database and Detection Triage Dashboard.
- High detection severity, if matched IP address is the destination
- Low detection severity, if matched IP address is the source
Configuration Options🔗
This detector is enabled by default when the required data sources or integrations are available in the tenant.
MITRE ATT&CK Category🔗
This detector has no MITRE Mapping.
Detector Testing🔗
This detector does have a supported testing method.
FROM detection WHERE metadata.creator.detector.detector_id='app:detect:threat-intel-enrichment-netflow'
See Detector Test Detections - Netflow Threat Intel.
References🔗
- Schema