Darktrace🔗
以下は、Darktraceを設定してSecureworks® Taegis™ XDRへのログ取り込みを実現するための手順です。
接続要件🔗
| ソース | 宛先 | ポート/プロトコル |
|---|---|---|
| Darktrace | Taegis™ XDR Collector (mgmt IP) | TCP/601 |
インテグレーションから提供されるデータ🔗
| 正規化されたデータ | 汎用的な検知 | ベンダー固有の検知 | |
|---|---|---|---|
| Darktrace | Thirdparty |
注意
XDR検知機は、データソースのログが特定の検知機に関連付けられたスキーマへ正規化されていても、必ずしもトリガーされるとは限りません。ただし、カスタム検出ルールを作成することで、データソースから正規化されたデータに基づいて検知を生成することができます。
Darktraceプラットフォームの設定🔗
注意
Portalアクセス権を持つDarktrace管理者が、DarktraceからXDR Collectorへsyslogを送信するように設定する必要があります。
Darktraceでsyslog転送を設定するには、以下の手順に従ってください。
- Darktrace Portalにログインします。
- Threat Visualizer内で、Admin > System Config に移動します。
- 左側のメニューからModulesを選択し、利用可能なWorkflow IntegrationsからSyslogを選択します。
- 設定ウィンドウでSyslog JSONを選択し、Newをクリックして設定画面を開きます。
- JSON Syslog Alertsフィールドをtrueに設定します。
- JSON Syslog Serverフィールドに、XDR CollectorのIPアドレスを指定します。
- JSON Syslog Server Portフィールドに601を指定します。
- JSON Syslog TCP Alertsフィールドをtrueに設定します。
クエリ言語検索例🔗
過去24時間のthirdpartyイベントを検索するには:
`FROM thirdparty WHERE sensor_type = 'DARKTRACE_SYSLOG' and EARLIEST=-24h`
source IPアドレスが10.1.1.10のthirdpartyイベントを検索するには:
`FROM thirdparty WHERE sensor_type = 'DARKTRACE_SYSLOG' and source_address = '10.1.1.10'`
thirdpartyの「Unusual Activity」イベントを検索するには:
`FROM thirdparty WHERE sensor_type='DARKTRACE_SYSLOG' AND summary contains 'Unusual Activity::'`
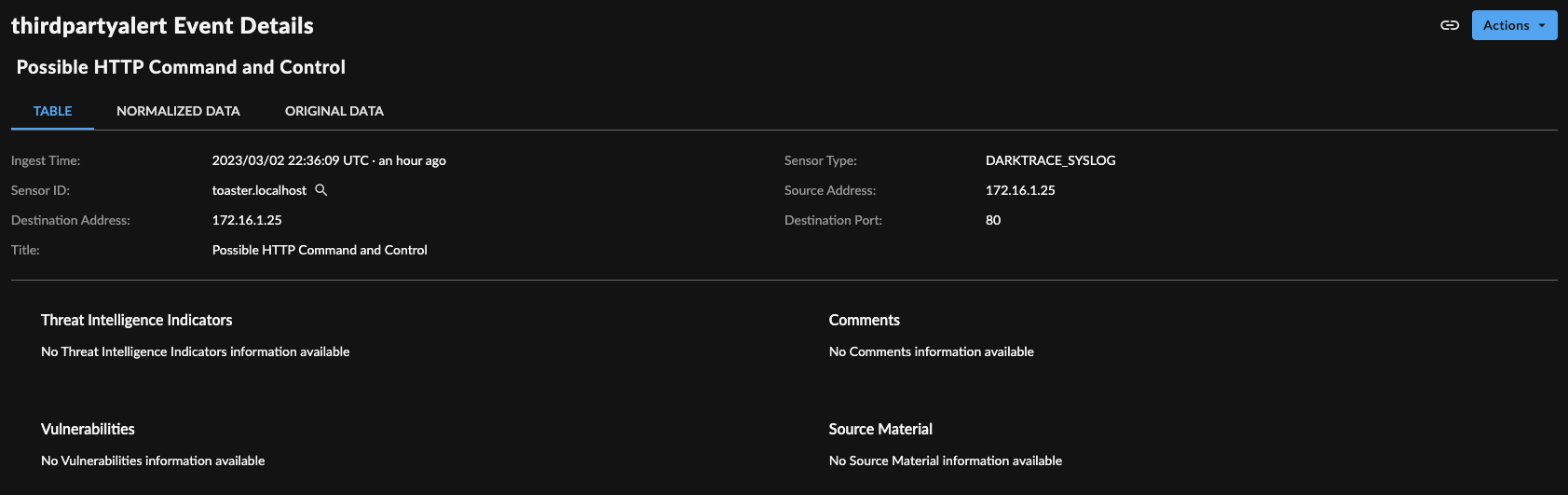
イベント詳細🔗
サンプルログ🔗
アラート🔗
{"creationTime":1597314595000,"breachUrl":"https://dt.corp.internal/#modelbreach/99104","commentCount":0,"pbid":99104,"time":15972312590000,"model":{"name":"Anomalous File::Internal::Additional Extension Appended to SMB File","pid":6,"phid":1757,"uuid":"e9f0ca2b-fac5-abc3-b5e4-a0e70f0ff024","logic":{"data":[{"cid":3647,"weight":1},{"cid":3646,"weight":1}],"targetScore":1,"type":"weightedComponentList","version":1},"throttle":3600,"sharedEndpoints":false,"actions":{"alert":true,"antigena":{},"breach":true,"model":true,"setPriority":false,"setTag":false,"setType":false},"tags":["AP: Lateral Movement","AP: Exploit"],"interval":3600,"sequenced":false,"active":true,"modified":"2020-02-11 11:12:02","activeTimes":{"devices":{},"tags":{},"type":"exclusions","version":2},"priority":4,"autoUpdatable":true,"autoUpdate":true,"autoSuppress":true,"description":"A device is renaming files on a network share with an additional extension - for example file.doc to file.doc.crypted. This activity is commonly seen during ransomware encryption events.\\n\\nAction: Review the breach log and the device's event log to review the files being renamed and look for any suspicious file extensions being added.","behaviour":"decreasing","defeats":[],"created":{"by":"Unknown"},"edited":{"by":"System"},"version":48},"triggeredComponents":[{"time":1593214589000,"cbid":113208,"cid":3647,"chid":5349,"size":6,"threshold":5,"interval":300,"logic":{"data":{"left":"A","operator":"AND","right":{"left":"B","operator":"AND","right":"C"}},"version":"v0.1"},"metric":{"mlid":296,"name":"smbmovesuccess","label":"SMB Move Success"},"triggeredFilters":[{"cfid":34511,"id":"d3","filterType":"Unusual SMB usage","arguments":{},"comparatorType":"display","trigger":{"value":"0"}},{"cfid":34512,"id":"d2","filterType":"Message","arguments":{},"comparatorType":"display","trigger":{"value":"share=\\\\COMPANYSERVER\\DOCS file=Store\\PAS\\SALES_FORECAST.doc rename=Store\\PAS\\SALES_FORECAST.dat version=smb2"}},{"cfid":34513,"id":"d1","filterType":"Internal destination device name","arguments":{},"comparatorType":"display","trigger":{"value":"corpfs01.corp.internal"}},{"cfid":34514,"id":"C","filterType":"Message","arguments":{"value":"\\fstmp\\"},"comparatorType":"does not contain","trigger":{"value":"share=\\\\COMPANYSERVER\\DOCS file=Store\\PAS\\SALES_FORECAST.doc rename=Store\\PAS\\SALES_FORECAST.dat version=smb2"}},{"cfid":34515,"id":"B","filterType":"Direction","arguments":{"value":"out"},"comparatorType":"is","trigger":{"value":"out"}},{"cfid":34516,"id":"A","filterType":"Message","arguments":{"value":"/.*file=(.*)\\srename=\\1\\.(?!([^\\s]*\\.)?(~PSTMP|bak|_01_|sent|pslock|cvr|00|backup|old|tmp|delete|del\\d{0,3}|fnb\\d{5}|sb-[[:xdigit:]]{8}-[[:alnum:]]{6}(?:\\\\[A-F0-9]{8})?|wrk[0-9]*|utbak|tmp[0-9]*|tftp|saf|_rq|reada_processing|old[0-9]*|mssdel|in_dev|PROCESSING|20[12][0-9-]{5,}|done|orig|bak5[0-9a-z]{7}|SPCDL_Processing|PendingOverwrite|DeletePending|ii|IFP|processed)(\\s.*|$))[^\\s]+(\\sversion.*|$)/i"},"comparatorType":"matches regular expression","trigger":{"value":"share=\\\\COMPANYSERVER\\DOCS file=Store\\PAS\\SALES_FORECAST.doc rename=Store\\PAS\\SALES_FORECAST.dat version=smb2"}}]}],"score":0.809,"device":{"did":18752,"macaddress":"00:01:02:aa:bb:cc","vendor":"Dell Inc.","ip":"10.1.2.3","ips":[{"ip":"10.1.2.3","timems":1591048400000,"time":"2020-08-12 05:00:00","sid":350}],"sid":350,"hostname":"bobs-palm-pilot.corp.internal","firstSeen":1581315366000,"lastSeen":1595210105000,"typename":"laptop","typelabel":"Laptop","credentials":["bob"],"tags":[{"tid":21,"expiry":0,"thid":44,"name":"Domain Authenticated","restricted":false,"data":{"auto":false,"color":200,"description":""},"isReferenced":true}]}}
AI Analyst🔗
{"userTriggered":false,"relatedBreaches":[{"modelName":"Compromise / Fast Beaconing to DGA","pbid":83856,"timestamp":1647581599000,"threatScore":69}],"summariser":"HttpAgentSummary","details":[[{"contents":[{"key":"Source device","values":[{"mac":"00:23:63:aa:bb:cc","did":3333,"ip":"172.16.1.25","subnet":"Allen","identifier":null,"sid":35,"hostname":null}],"type":"device"}],"header":"Device Making Suspicious Connections"}],[{"contents":[{"key":"User agent","values":["Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/536.5 (KHTML, like Gecko) Chrome/19.0.1084.52 Safari/536.5"],"type":"string"}],"header":"Suspicious Application"},{"contents":[{"key":"Time","values":[{"start":1646660731572,"end":1647584551989}],"type":"timestampRange"},{"key":"Hostname","values":[{"ip":null,"hostname":"host.domain.com"}],"type":"externalHost"},{"key":"Hostname rarity","values":[100],"type":"percentage"},{"key":"Hostname first observed","values":[1572162214000],"type":"timestamp"},{"key":"Most recent destination IP","values":[{"ip":"1.2.3.4","hostname":"1.2.3.4"}],"type":"externalHost"},{"key":"Most recent ASN","values":["AS12309 BNBAPO-02"],"type":"string"},{"key":"Total connections","values":[8174],"type":"integer"},{"key":"URI","values":["/uqot/aqoy.php?cmd=reg_server&uid=MZXSD353R66RB3AE111A"],"type":"string"},{"key":"Port","values":[80],"type":"integer"},{"key":"HTTP method","values":["GET"],"type":"string"},{"key":"Status codes","values":["200","504"],"type":"string"}],"header":"Suspicious Endpoints Contacted by Application"}]],"aiaScore":59.42524877702945,"children":["bc9ee386-33ec-4061-b923-964dca2e5190"],"externalTriggered":false,"groupByActivity":false,"attackPhases":[2],"summary":"The device 172.16.1.25 was observed making multiple HTTP connections to the rare external endpoint host.domain.com, with the same user agent string.\n\nMoreover, this device only used this user agent for connections to a limited set of endpoints - suggesting that the activity was initiated by a standalone software process as opposed to a web browser.\n\nIf such behaviour is unexpected, further investigation may be required to determine if this activity represents malicious command and control as opposed to legitimate telemetry of some form.","acknowledged":false,"activityId":"cd604490","breachDevices":[{"mac":"00:23:63:aa:bb:cc","did":3333,"ip":"172.16.1.25","subnet":"Allen","identifier":null,"sid":35,"hostname":null}],"id":"bc9ee386-33ec-4061-b923-964dca2e5190","title":"Possible HTTP Command and Control","groupingIds":["f56d6351"],"pinned":false,"periods":[{"start":1646660731572,"end":1647584551989}]}